There are always new attempts by governments to systematically monitor Internet users for no reason. However, mass surveillance is not only unsuitable for fighting crime, it is also completely incompatible with democratic principles and poses a considerable threat to data security.
Lire la suite...
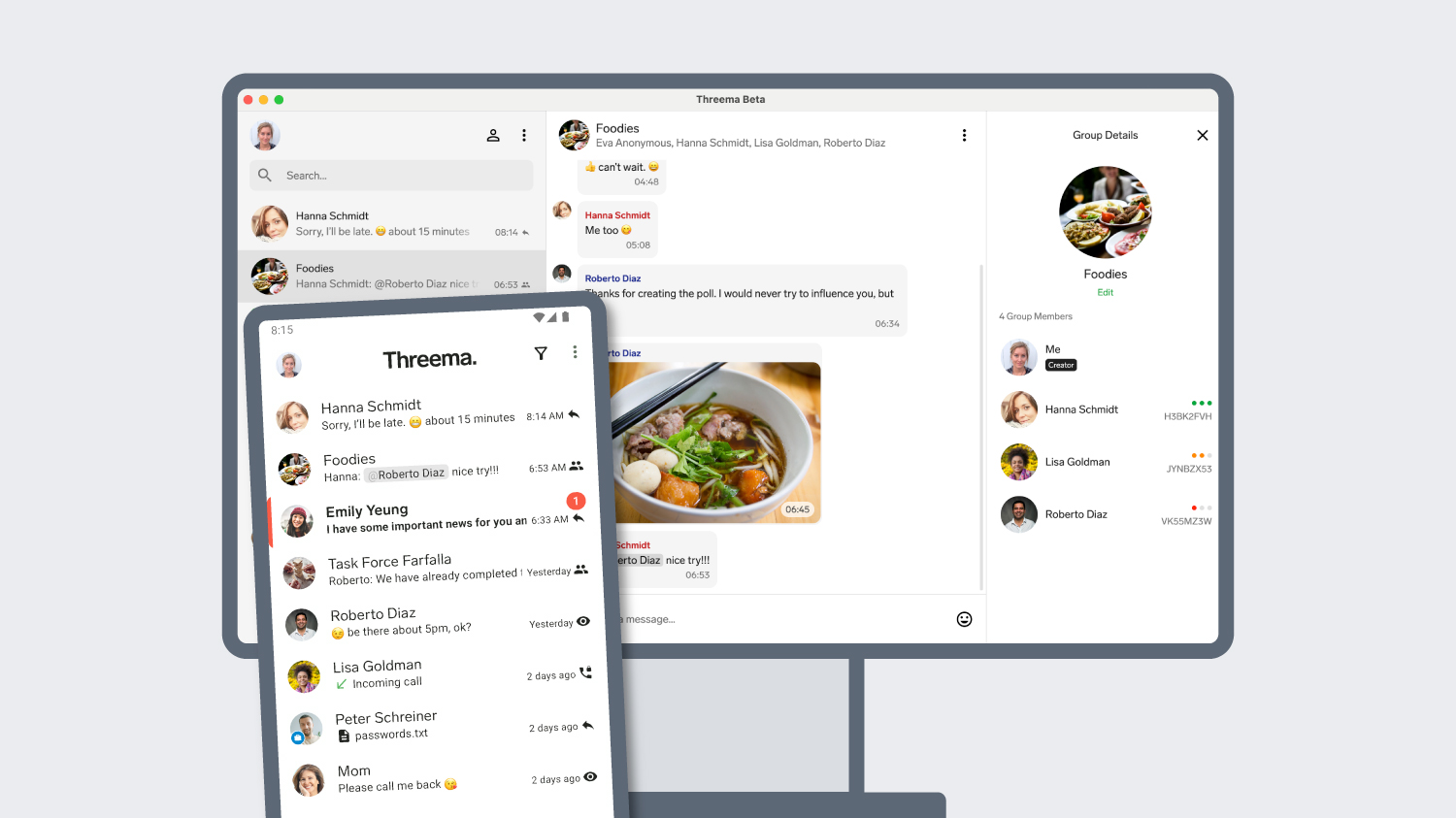
Good news for Android users who like to chat from the computer: the beta version of Threema’s new desktop app (which was already available to iOS users) can now also be linked to Android devices.
Lire la suite...
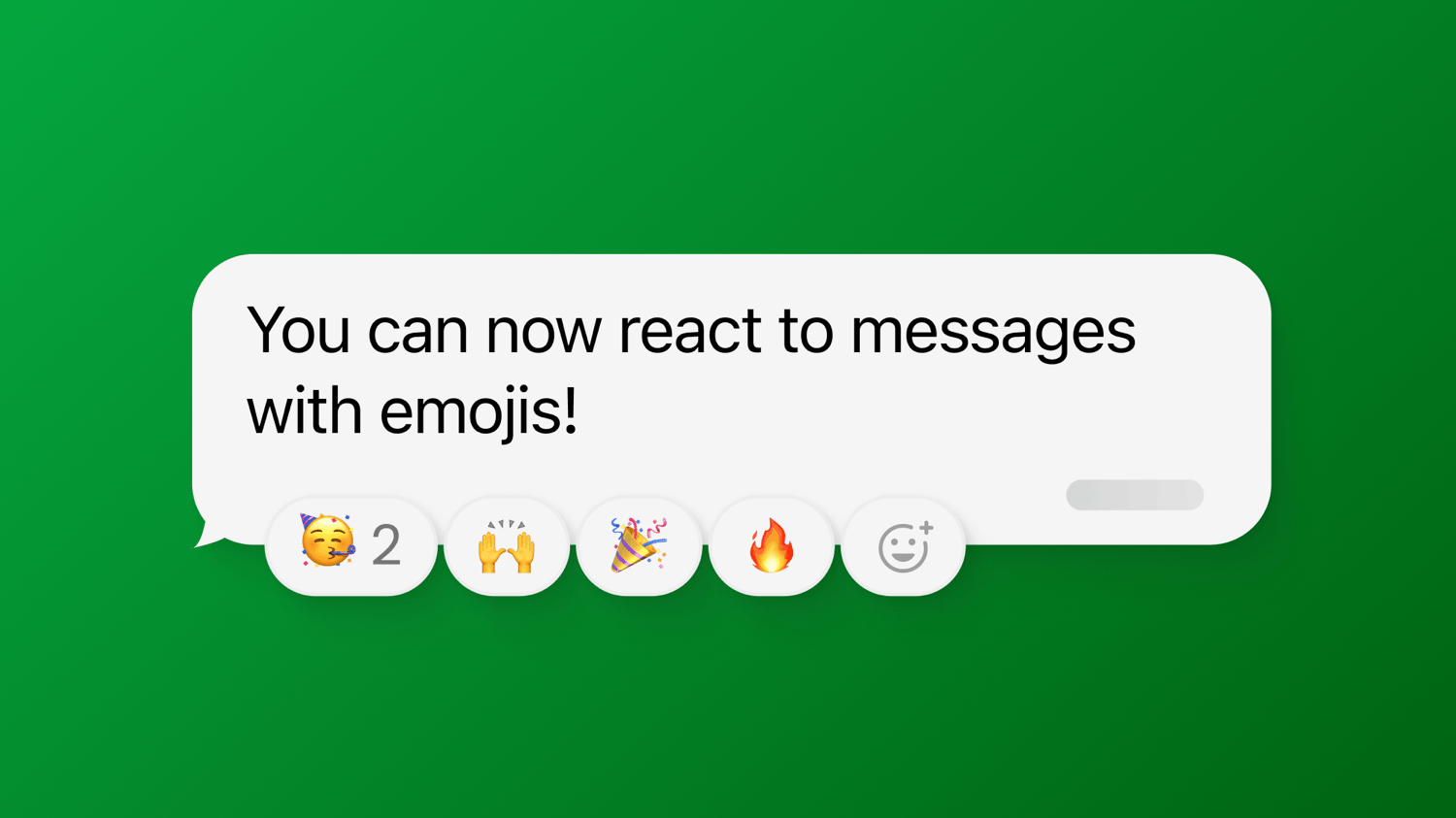
What a nod or a shake of the head conveys in a face-to-face conversation can be replicated in Threema with the agree/disagree feature. Sometimes, however, a “thumbs up” or “thumbs down” isn’t enough to express how we feel about a message. That’s where the new emoji reactions come in.
Lire la suite...
Nearly a year has passed since the so-called “gatekeepers” had to prove their compliance with the European Union’s Digital Markets Act (DMA). Yet, some of them are still bypassing the law.
Lire la suite...
January 28 is Data Privacy Day. To celebrate this awareness day, we’ve created a sticker collection dedicated to online privacy. Show your support for the cause, and personalize your smartphone or laptop with privacy stickers!
Lire la suite...
The source code of Threema’s new desktop app is now publicly accessible. Consequently, the app is also covered by Threema’s bug bounty program. However, bounty hunters shouldn’t get too excited: the new desktop app has already undergone a thorough security audit, and it passed a recent bug bounty challenge.
Lire la suite...
Exactly twelve years ago today, on 12/12/2012, the first Threema version was published in Apple’s App Store, laying the foundation for secure and privacy-friendly mobile communication.
Lire la suite...
Like Threema, Apostrophy is a Swiss company that puts privacy first, doesn’t collect user data, and opposes to Big Tech’s ad-driven business model. Now, the two companies team up to facilitate secure and privacy-compliant mobile communication.
Lire la suite...
Together with Epic Games, Proton, and various other companies, we urge the European Parliament to not let Apple’s and Google’s circumvention of the Digital Markets Act (DMA) slide.
Lire la suite...
As the name implies, instant messaging is a fast-paced means of communication. This characteristic has numerous advantages – but also a few disadvantages: due to the fast pace, typos are the rule rather than the exception, and, what’s worse, sometimes messages get sent to the wrong contact in the heat of the moment.
Lire la suite...
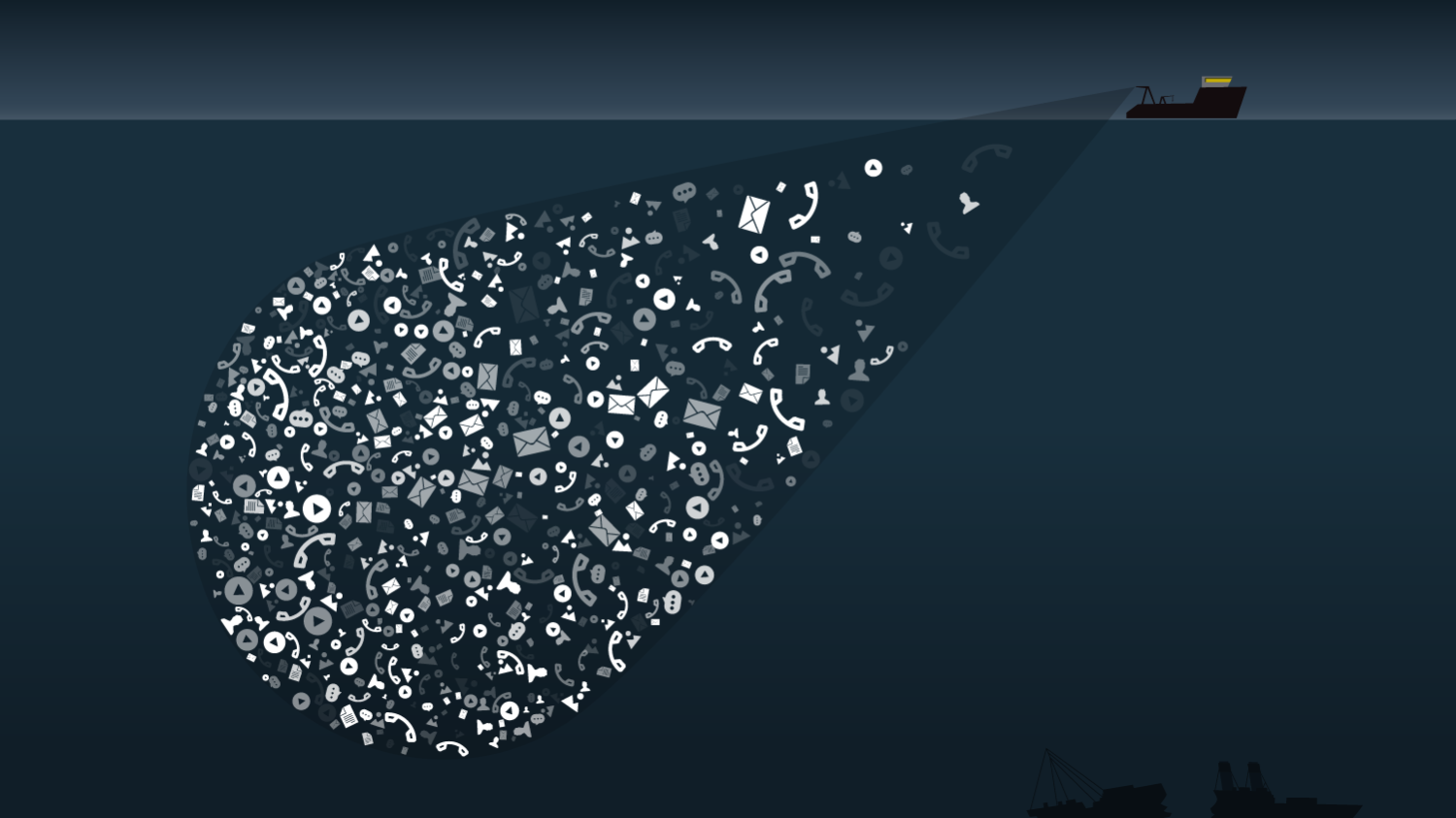
Preserving privacy on the Internet isn’t easy: advertisers are finding ever more sophisticated ways to collect user data, and new, convenient technology detracts from the negative impact on privacy. The resulting decline in online privacy is further fueled by the fact that online privacy can, due to its abstract nature, be quite hard to grasp.
Lire la suite...
Mobile instant messengers became popular as a replacement for SMS messages. Today, they are one of the most widely used Internet services and are no longer limited to written communication – voice messages and video calls are now just as much a part of chat apps as text messages.
Lire la suite...
As highlighted by recent news stories and social media posts, the desktop apps of some messaging services are affected by a long-standing security issue. We’ve been asked whether Threema’s desktop client also suffers from this or any similar flaw. The short answer: No. Threema users don’t need to take any precautions and can continue to use the desktop app. The longer, more explanatory answer:
Lire la suite...
With its legislative proposal known as “Chat Control,” the EU Commission is trying to establish an unprecedented mass-surveillance apparatus of Orwellian proportions in the European Union. If EU citizens don’t stand up for privacy now, it may be too late.
Lire la suite...
The cybersecurity expert Bruce Schneier has recently published an interesting blog post in which he (together with co-author Barath Raghavan) argues that online privacy is continuing to decline for the same reason overfishing occurred in the last century – due to the “Shifting Baseline Syndrome.” The presented analogy is a powerful one, but we still feel that it falls flat in some regards, and in reality, online privacy might even be worse off than suggested.
Lire la suite...